A marketer’s guide to three security research types
Updated 2026-04-21
A simple framework for classifying security research as intelligence, vulnerability, or attack and tradecraft before legal and engineering review. Label the story before you approve copy or a press release. Mixing all three on one page confuses reviewers and weakens approvals.

The three research modes (pick one lead)
Cybercrime intelligence: actors, campaigns, underground economics, victimology - who profits and how infrastructure moves.
Vulnerability discovery: defects, severity, affected versions, patches, and vendor coordination.
Attack research: techniques, kill chain, observable behaviors - often mappable to frameworks like MITRE ATT&CK for clarity.
Your external comms should have one lead mode per major asset; supporting mentions of the others are fine in sub-bullets if labeled clearly.
One incident, three lenses - don’t blend them in one headline
A single breach story can touch all three: analysts talk about the group, engineers debate the vuln, and IR reconstructs the attack path. Marketing wins when you choose the lead narrative for the audience (e.g. executives vs. practitioners) and keep the other angles in supporting detail or separate pieces.
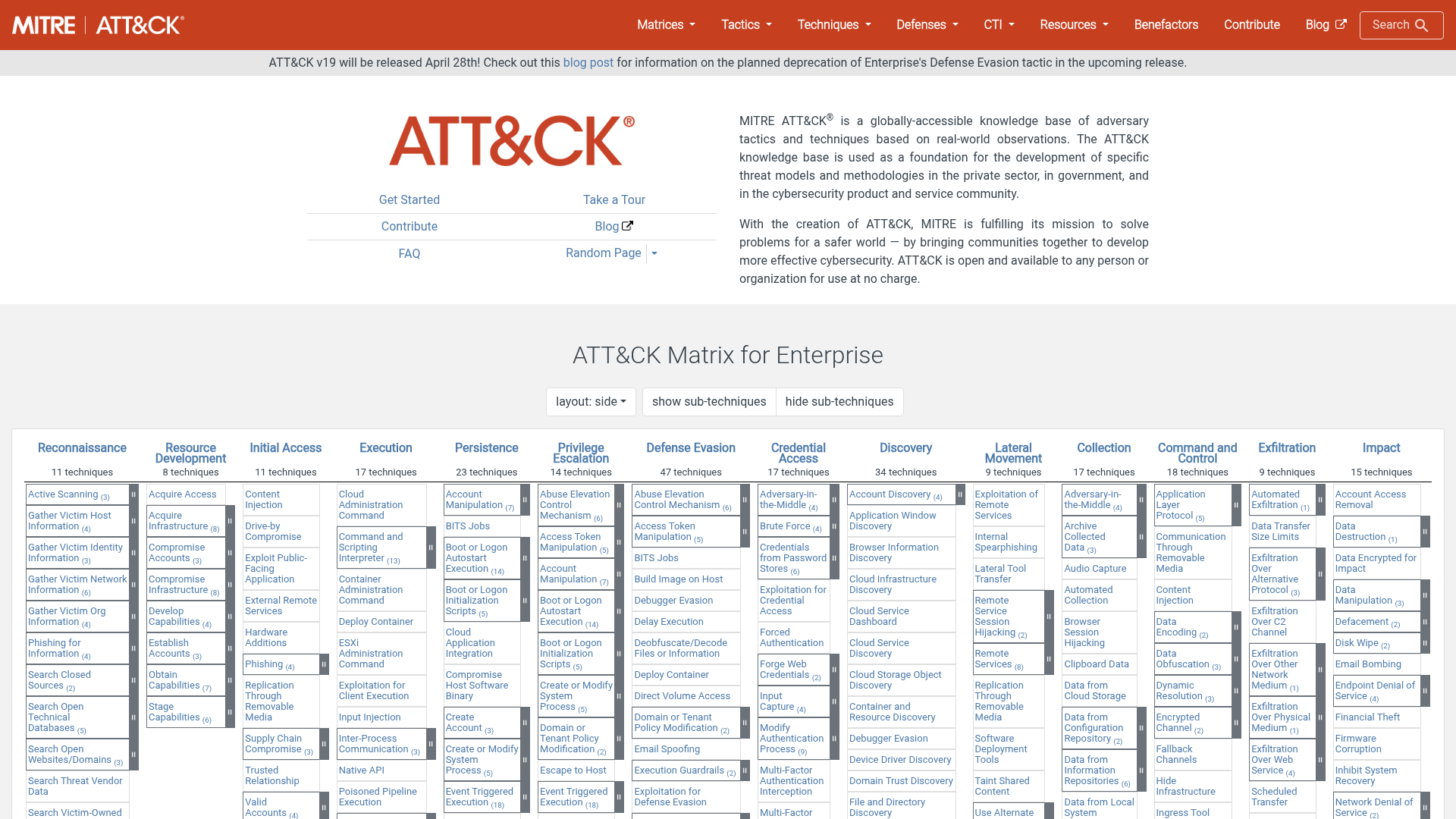
Attack and tradecraft framing (MITRE ATT&CK as a shared language)
When you describe how intrusions work, prefer observable behaviors and, where useful, MITRE tactics/techniques so practitioners can map your claims to their detection stack. Avoid vague “sophisticated APT” language without specifics.
List the techniques you can actually cite from your research or vendor reporting, then write to that list—nothing in the headline should fail a technical review.
MITRE ATT&CK: knowledge base.
Screenshot
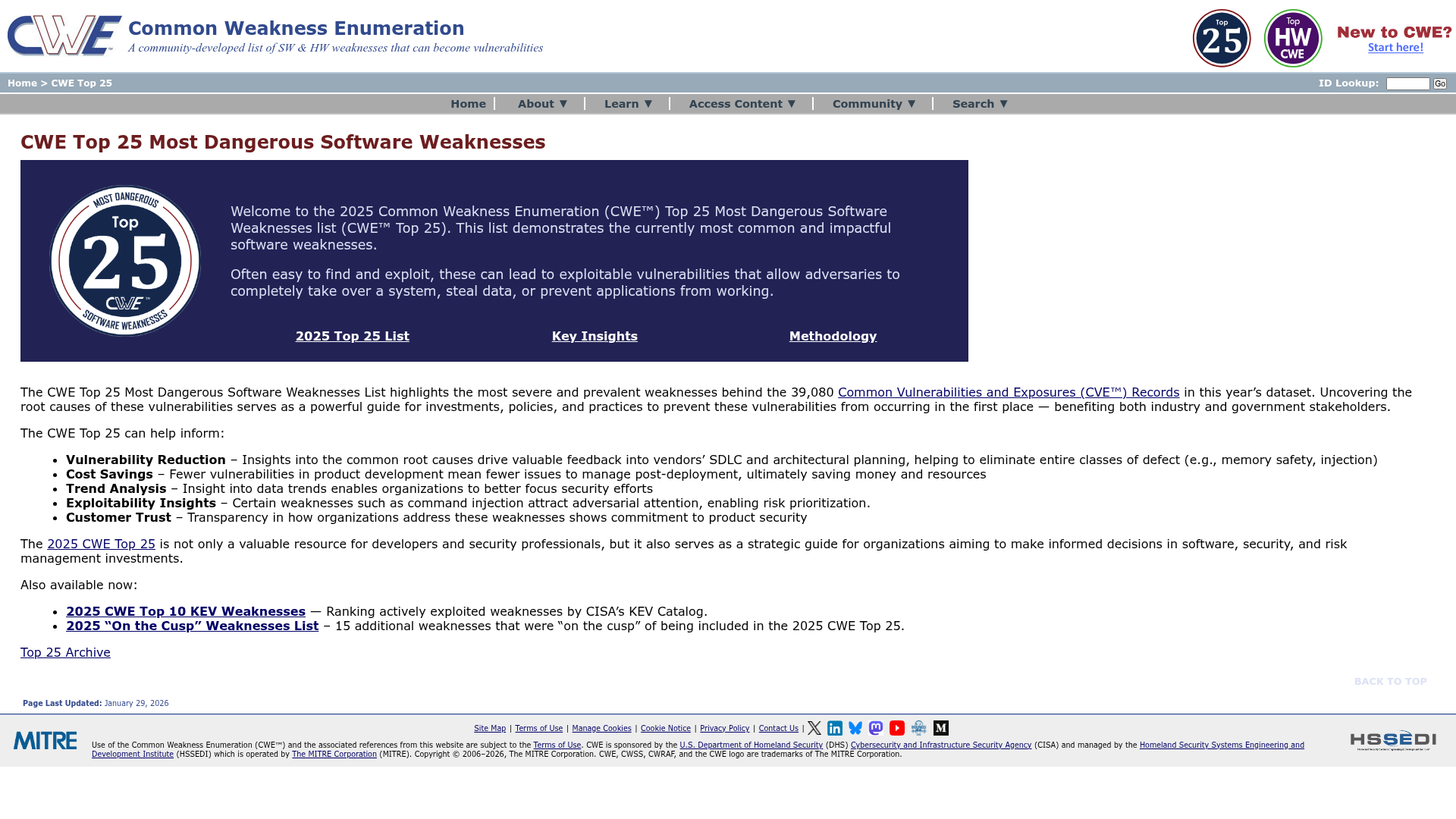
Vulnerability framing (severity, scope, and patch reality)
Vulnerability stories draw scrutiny on CVSS, affected products, and patch timelines. State what is confirmed vs. inferred. If scope is narrow, say so - overclaiming “everyone is affected” backfires when the community debunks it.
CWE Top 25 and similar references help classify weakness types when your story is about classes of bugs, not a single CVE.
Screenshot
Messaging checkpoints (use before you ship)
Do we have primary material (samples, timelines, reproduction steps) or only third-party writeups?
Who signed off - security research, legal, and comms - and on what assumptions?
What is the reader supposed to do next: patch, reconfigure, validate coverage, or talk to sales - and is that CTA honest for the story we told?
Common questions
What are the three types of security research in this guide?
Cybercrime intelligence (actors, campaigns, underground economics), vulnerability discovery (defects, severity, patches), and attack or tradecraft research (techniques, kill chain, behaviors). Pick one lead mode per major asset.
Why should I avoid blending all three research types in one headline?
One incident can touch intelligence, vulnerabilities, and attack paths, but readers and reviewers need a single lead narrative. Mixed headlines make claims harder to defend in technical review.
What is MITRE ATT&CK used for in this context?
It gives practitioners a shared language for tactics and techniques when you describe how intrusions work. Use it to align marketing language with detection and engineering teams.
What should I check before shipping vulnerability-related messaging?
Confirm what is verified versus inferred, state scope and patch status clearly, and avoid overstating affected populations. Overclaiming invites public correction.